Incident Unveils Risks of Source Map Configuration
Recent news surrounding Claude Code, used daily by developers, revealed an alarming incident: a configuration oversight exposed the original TypeScript source code without any hacking involved. As noted, “
No one hacked Anthropic. The system did exactly what it was configured to do.”
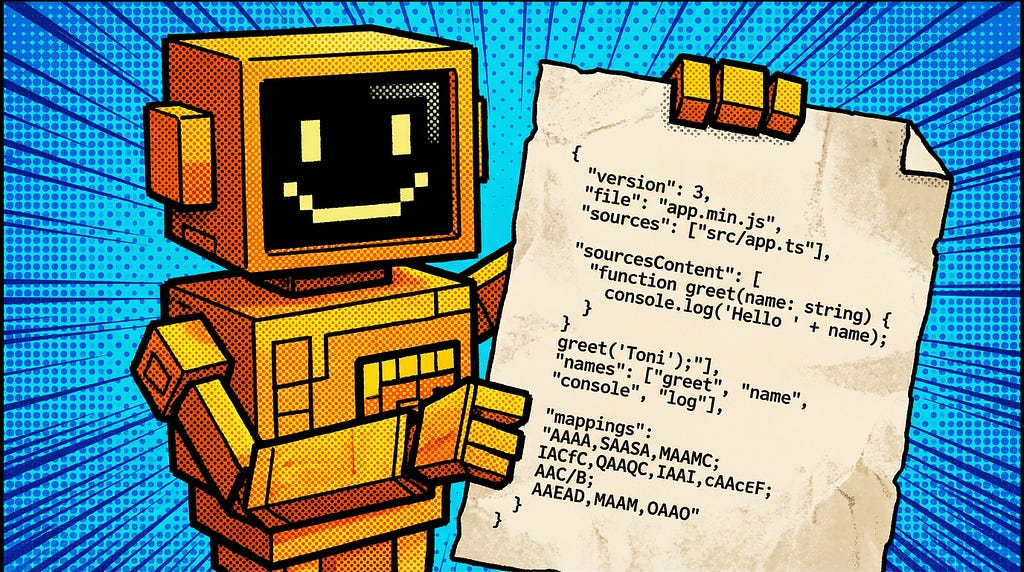
This incident underscores a recurring theme in software development: the most critical failures often stem from innocent configuration mistakes rather than malicious attacks. When shipped, source maps should not compromise security. They help relate minified code back to its original form, but the way they’re set up can bring varying levels of risk:
- Level 1: Mapping only—low risk.
- Level 2: Mapping + external source—moderate risk.
- Level 3: Embedded source—high risk, leading to the exposure seen here.
The key takeaway? Treat source map configurations as crucial security decisions. Before your next deployment, ask:
- What type of source map is being generated?
- Are these maps included in your package?
- What does the published artifact actually contain?
- Do you have checks in place for embedded content?
In a landscape where convenience can mask risk, understanding these details is essential. What might you be overlooking in your build pipeline? For more insights, explore the full article!
Read the full story for more details:
Continue reading